Compliant-by-design with the Chino.io Tech Toolkit
The Chino.io platform provides a set of modules to make your digital health project GDPR or HIPAA compliant.
Solve complex and risky compliance tasks, deliver your projects globally.






& Authorization
& Key Management
The only cloud platform certified for ISO 13485, 27001, and 9001—ready for regulated software.
Stay on track with a guided, expert-led process that eliminates friction and empowers your team every step.
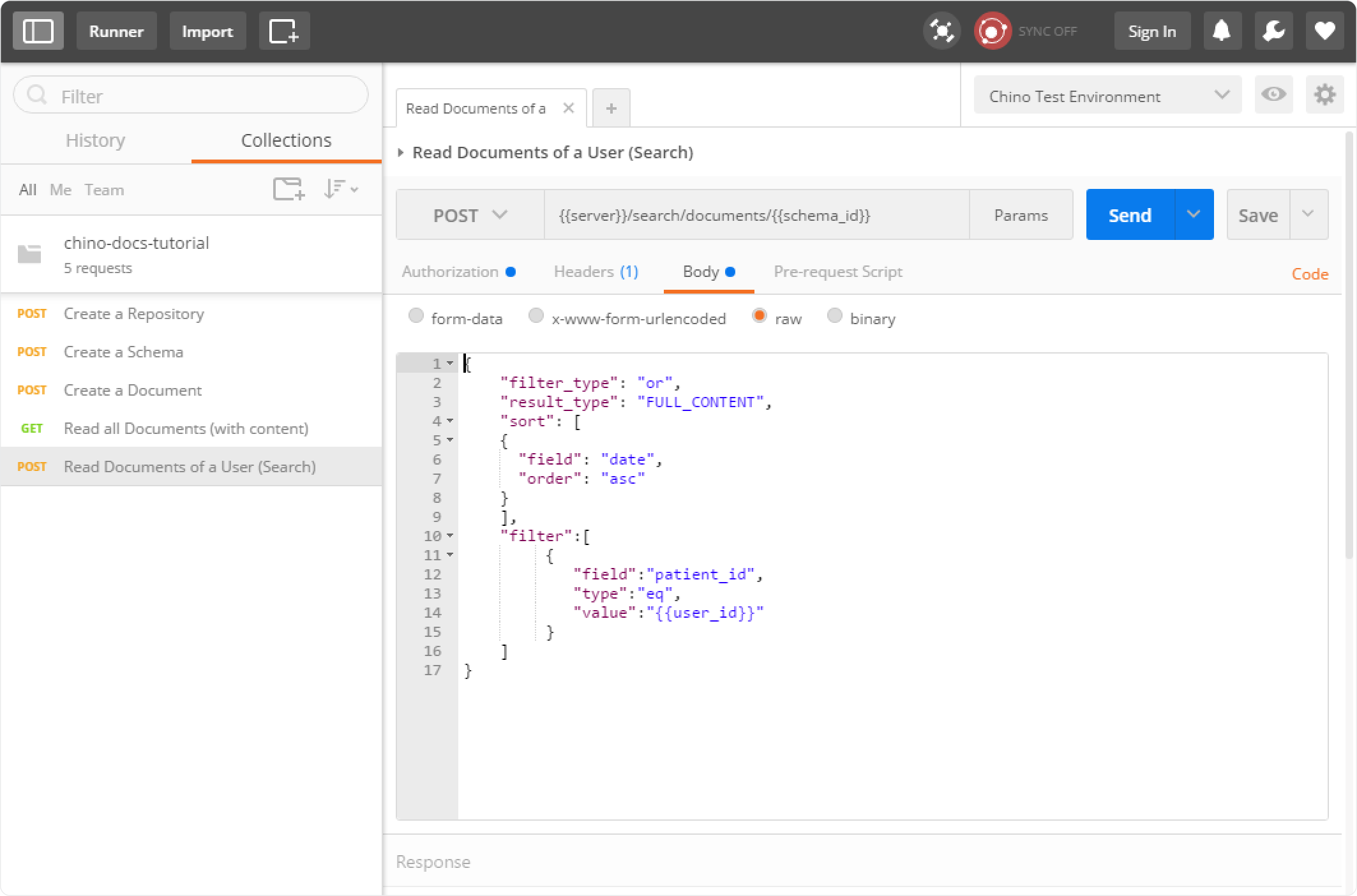
Data Security
Store encrypted health data like records or scans with one API. Chino.io meets GDPR, HIPAA, and more, so you can build without worrying about compliance.
Secure User Management & Data Sharing
Manage users with access control, permissions, and logging. Store and share health data securely, and stay fully compliant.
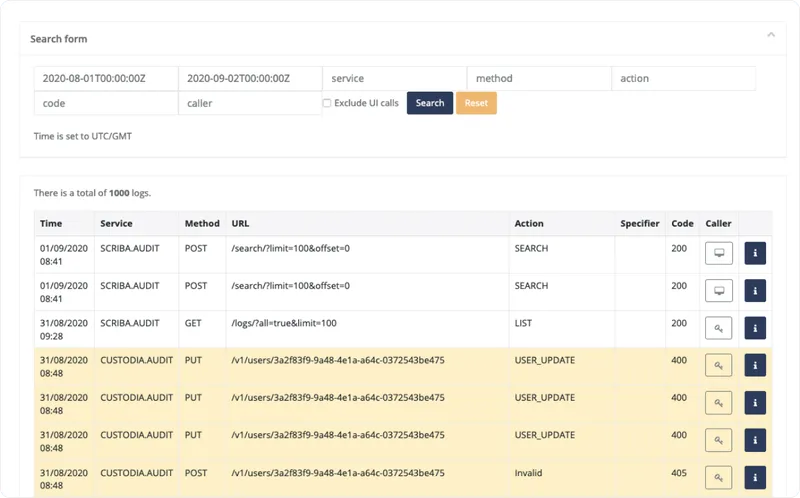
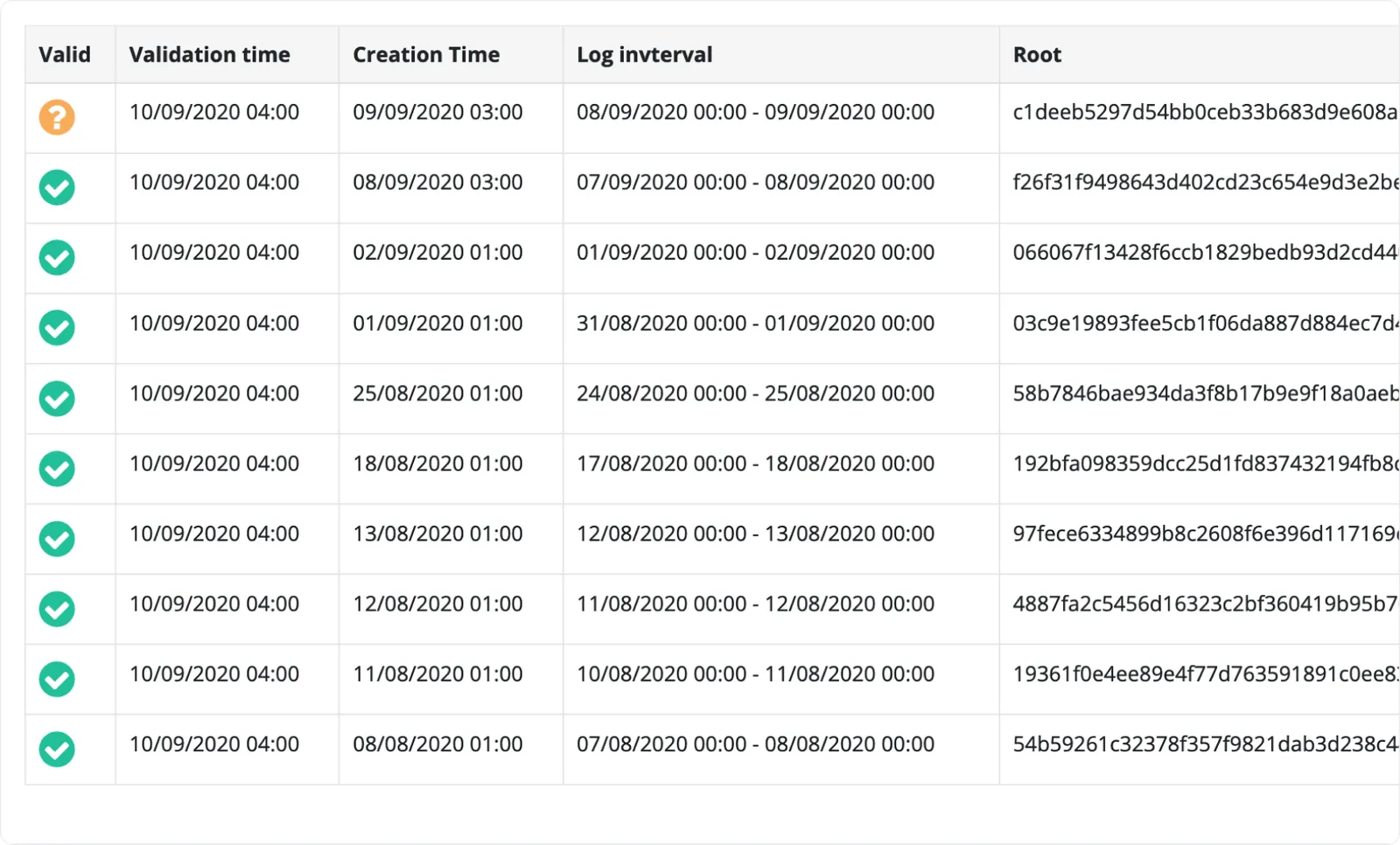
Verifiable Audit Logs & Monitoring
Get automatic, immutable audit logs that meet GDPR, HIPAA, and FDA. Track every action, add events, and trigger alerts with full legal traceability.
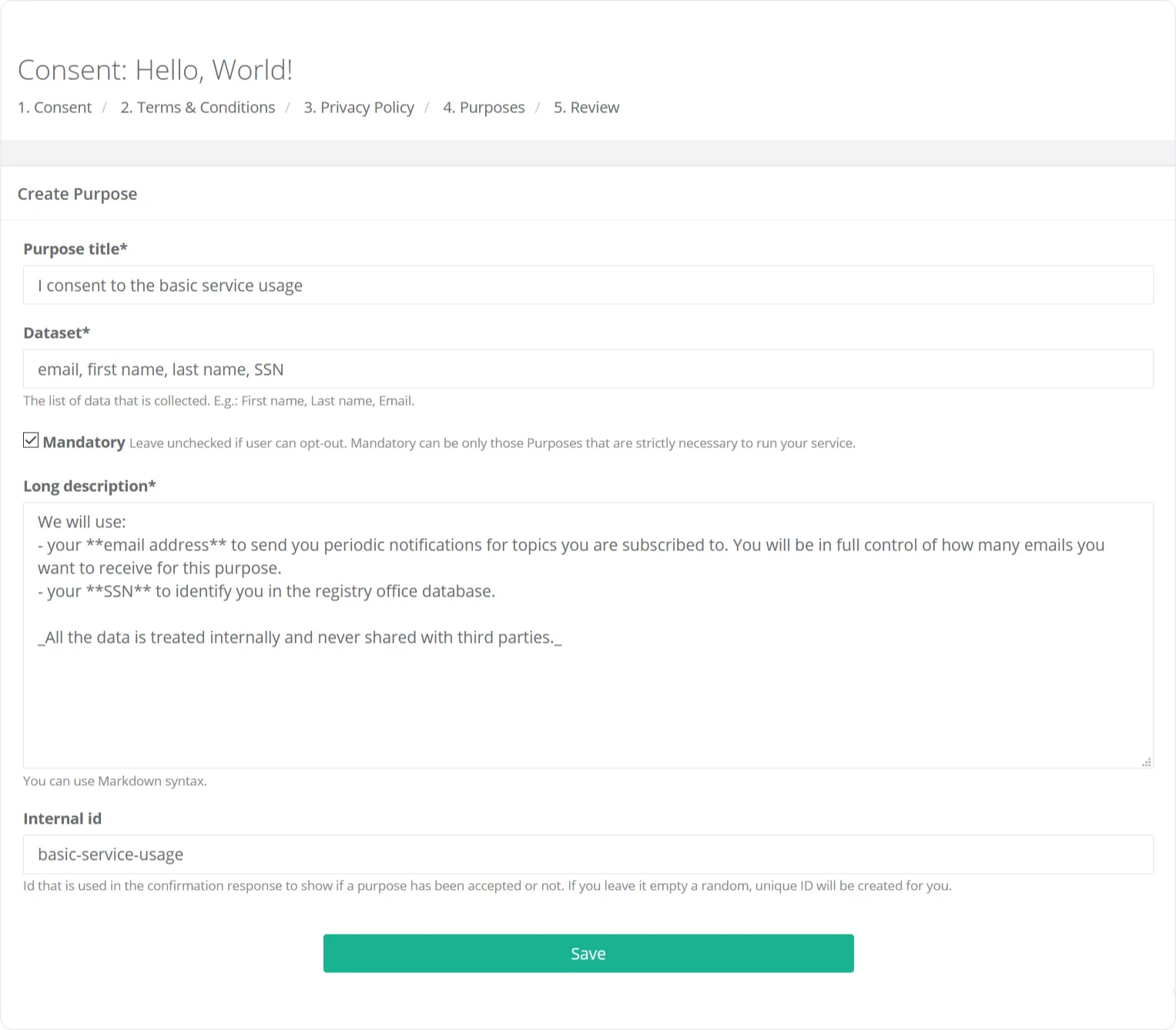
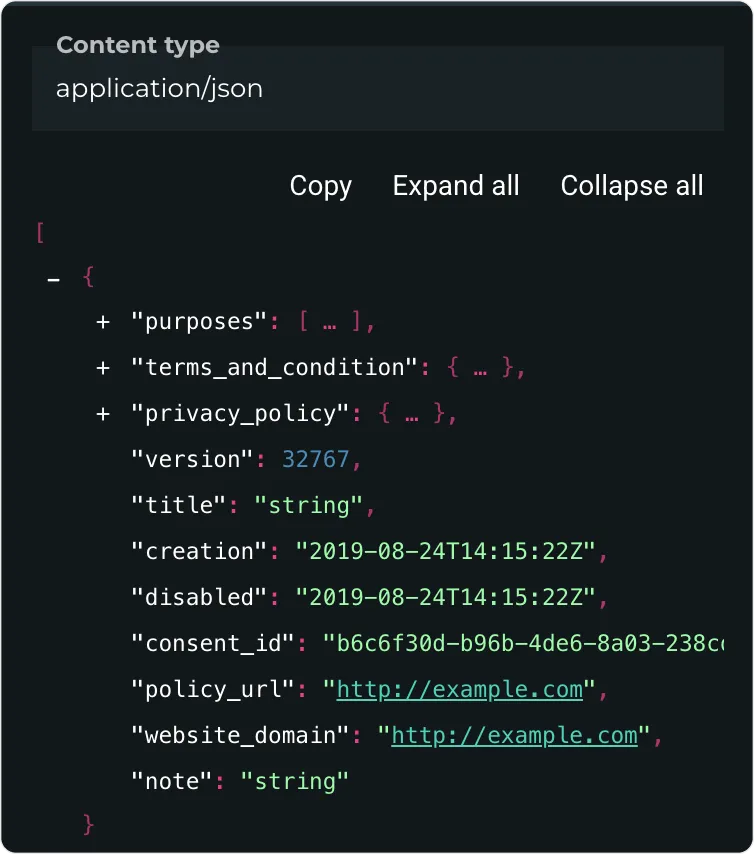
User Consent Management
Collect, sync, and track consents with full GDPR compliance. See what users agreed to, when, and stay ready for audits or data subject requests.
You Choose the Setup
We offer cloud and custom installations. You always retain full control over your data.







“The beauty of working with Chino.io is their problem-solving approach. They are always available when we need.”
Let Us Take the Weight Off Your Shoulders
The Chino.io team helps you manage compliance with expert guidance.
- Navigate compliance requirements, tailored to you.
- Prepare for standards like ISO 27001, HIPAA and more.
- Scale your compliance efforts as your business does.
- Reduce time to market through guaranteed GDPR compliance
Cover all required regulations and standards
Advice and support for all relevant data protection, legal, and security frameworks—GDPR, HIPAA, AI Act, NIS2, DVG/DiGA, ISO27001, C5 and many more.

GDPR
GDPR
Comply with EU's data privacy rules for handling personal information.

HIPAA
HIPAA
Meet US healthcare security standards for patient data.

ISO27001
ISO27001
Achieve global gold-standard information security management.

NIS2
NIS2
Comply with stricter EU
cybersecurity requirements.

DTx
DTx
Secure regulatory approval for digital therapeutic software.

AI Act
AI Act
Align with EU's risk-based AI regulations.

C5
C5
Comply with strict German cloud infrastructure security rules.

GDPR
GDPR
Comply with EU's data privacy rules for handling personal information.

HIPAA
HIPAA
Meet US healthcare security standards for patient data.

ISO27001
ISO27001
Achieve global gold-standard information security management.

NIS2
NIS2
Comply with stricter EU
cybersecurity requirements.

DTx
DTx
Secure regulatory approval for digital therapeutic software.

AI Act
AI Act
Align with EU's risk-based AI regulations.

C5
C5
Comply with strict German cloud infrastructure security rules.

DTx
DTx
Secure regulatory approval for digital therapeutic software.

AI Act
AI Act
Align with EU's risk-based AI regulations.

C5
C5
Comply with strict German cloud infrastructure security rules.

GDPR
GDPR
Comply with EU's data privacy rules for handling personal information.

HIPAA
HIPAA
Meet US healthcare security standards for patient data.

ISO27001
ISO27001
Achieve global gold-standard information security management.

NIS2
NIS2
Comply with stricter EU
cybersecurity requirements.

DTx
DTx
Secure regulatory approval for digital therapeutic software.

AI Act
AI Act
Align with EU's risk-based AI regulations.

C5
C5
Comply with strict German cloud infrastructure security rules.

GDPR
GDPR
Comply with EU's data privacy rules for handling personal information.

HIPAA
HIPAA
Meet US healthcare security standards for patient data.

ISO27001
ISO27001
Achieve global gold-standard information security management.

NIS2
NIS2
Comply with stricter EU
cybersecurity requirements.
